If you’re like us and you like building things as much as we do, it’s a safe bet you have strong opinions about technology. Our Internet-enabled world has brought us fantastic innovations, including the ability to solve hard problems by working together through crowd-sourcing, new mechanisms for getting projects off the ground through crowd-funding, and unprecedented levels of convenience, comfort and entertainment thanks to myriad wearable devices, music players, smart phones and more. Like all technical innovations that come before — be it telegraph, telephone, or television — there has been a backlash. Technology advocates dismiss detractors as tech Luddites. In response, the Luddites say: this time it’s different.
How is the IoT Affecting Transportation?
And so, as the Internet we know today from our PCs, Macintoshes, iPhone and Android smart phones transmogrifies into a new era called the Internet of Things (or IoT for short), we have to ask the question: Is it different this time? Is this a step too far? Indeed there are many examples where new technologies are found to be dangerous. Back in the era of the telegraph, poor signaling technology caused trains to crash into each other on single rail tracks quite regularly. The boilers on passenger steamboats going up and down the Mississippi blew up on a regular basis, killing hundreds if not thousands. Even telegraph operators could be electrocuted by a direct-hit lightning strike to a telephone pole.
And — continuing with transportation examples — the fact that today’s statistically safest mode of transportation is flying through air underscores how much we owe to advances in modern technology that keeps us safe. Perhaps it’s this very trust that is the issue today. Because we now place such faith in modern technology — literally trusting it with our very own lives — it’s even more shocking when this very same technology can be used against us. As so often happens, Hollywood got there first. The suspense thriller movie Speed (where Keanu Reeves must disable a computer controlled bomb on a fast-moving Los Angeles city bus) presages many of the suspected or confirmed hacking attempts of our time.
For example, the mysterious loss of contact with Malaysian Airlines flight MH 370 was in the news again this week after a trailing edge ‘flaperon’ was found on the French island of Reunion east of Madagascar. The part is being investigated in France today to confirm if it came from the missing Boeing 777. Speculation on the missing plane has run rampant. Quite a number of people have weighed in saying that the exposed electronics bay of the Boeing 777 offers a unique opportunity to attach nefarious equipment and take control of the plane remotely.
Back in April, computer security researcher Chris Roberts tweeted: “Find myself on a 737/800, lets see Box-IFE-ICE-SATCOM, ? Shall we start playing with EICAS messages? “PASS OXYGEN ON” Anyone ? :)” While he made this suggestion in jest, the FBI took the notion very seriously and removed him posthaste from the United plane. After the incident, there was rampant discussion about whether what the unfortunate Mr. Roberts contemplated doing was even possible.

What Other Technologies Can Be Hacked?
But all this was before the above video went viral last week showing two enthusiastic hackers taking control of a Jeep Cherokee, including shutting down its engine at highway speeds and then later (in the safety of a parking lot) demonstrated disabling the brakes and interfering with the steering. Score one for the technology Luddites. Maybe this time it is different.
Before the argument against the Internet of Things went along these lines: Maybe having your refrigerator talk to the grocery store isn’t such a great idea after all, if they somehow conspired to surreptitiously curdle up the milk while you’re away at work. But it becomes altogether more serious if someone hacks into an airplane and flips it over, crashes your self-driving car, or locks all the doors in your office building… you get the idea.

To get a better appreciation of the risks versus the rewards, let’s take a look at what some hacking experts are saying. In the video above, hacker Pablos Holman gives a pretty honest appraisal about how risky our Internet-enabled life can be in his TEDx talk from two years ago. Among other things, he invites members of the audience to the stage where he hacks their credit card in front of their eyes before handing them a RFID resistant wallet.
Holman also talks about the ways that hackers can actually use their skills for good, such as creating large-scale ski the protection zones using video tracking technology and low powered lasers. Will the attraction of these “good” technology uses dissuade “black hat” hackers from wreaking havoc?
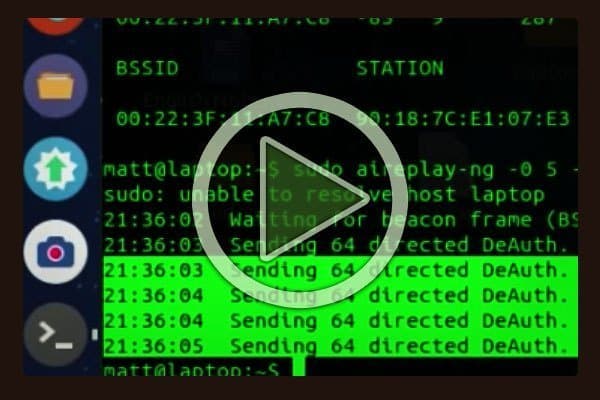
Probably not if the number of hacking how-to-guides appearing on YouTube is any indication. In the video above, you can learn how to hack into a common router, one of thousands of malware guides on the Internet. Disclaimer: in case there’s any doubt, we are not promoting these hacking activities, but only using them to illustrate our larger point that as the ever growing Internet of Things reaches nearly every device, appliance, hardware, tool and instrument, it poses a commensurately larger risk for all of us.
On the other hand, we don’t want to spin you up into a elevated state of paranoia. There are some practical things you can do to protect your own computer or smart phone, according to cyber security expert Frank Heidt. Heidt promotes two simple rules: First, turn on auto updates on your computer. Second, never use the same password on two different websites. That sounds like good advice to us.
Postscript One thing that struck us about the hacking examples we’ve used this week is that every single person represented is male. Where are the women? Isn’t that part of the problem you ask? Next time we will look at women in technology. We want to find out how campaigns like #iLookLikeAnEngineer are helping change the perceptions of women in high-tech, science and engineering workplaces.

Formaspace is Looking to the Future

We invite you to join the roster of satisfied Formaspace technical, manufacturing and laboratory furniture clients — including Apple Computer, Boeing, Dell, Eli Lilly, Exxon Mobile, Ford, General Electric, Intel, Lockheed Martin, Medtronic, NASA, Novartis, Stanford University, Toyota and more.
Give us a call today at 800.251.1505 to find out more about the Formaspace line of built-to-order computer workstations, industrial workbenches, laboratory furniture, lab benches and dry lab/wet labs — as well as our design / furniture consulting services. Like all Formaspace furniture, it’s backed by our famous 12 year, three shift guarantee.







