With many businesses closed to the public during the Covid-19 pandemic lockdown, online access has become a crucial economic lifeline, as millions of consumers have flocked to e-commerce websites and millions more have taken up working from home (WFH).
But this increased dependence on a reliable, robust online IT infrastructure carries its own costs.
According to the head of cybersecurity at CapGemini, worldwide spending on cybersecurity has reached $120 billion, and it’s expected to grow to $300 billion by 2024. Yet, despite this enormous outlay, CapGemini estimates that worldwide losses due to cyber fraud totaled $2 trillion during 2019. Another consulting firm, Accenture, projects the cost of cyber fraud will rise to $5.2 trillion worldwide within five years.
Over the years, many cyber-attacks have stayed on the down-low, to avoid public scrutiny for as long as possible. (Experts say creating a global standard for reporting cybercrime could help.)
But a series of high profile data breaches that put consumer data at risk has led to new governmental regulations obliging companies to come forward when customer data is exposed. The European GDPR (General Data Protection Regulation) is the most strict, penalizing companies with fines of up to 4% of annual turnover. (Fines for violating the new California Consumer Privacy Act are less severe, at up to $7,500 per incident.)
For smaller companies, the cumulative costs of a cyber-attack could literally put them out of business – permanently. Insurance carrier Hiscox reports that each cyber intrusion costs businesses $200,000 on average, while Chubb calculates that the average cost for a business to recover from a cyber-attack is $400,000.
Compounding the financial risk is whether you can even make a cybersecurity insurance claim at all; many carriers are now arguing that attacks by so-called “state actors” should be considered as an “act of war” – a category excluded by most insurance policy riders.
How the Coronavirus Pandemic has increased our Exposure to Cyber Crime
The Covid-19 pandemic has led to more employees working from home (WFM) as well as increased demand for e-commerce products and services, making this an ideal time for cyber criminals to attack corporate IT infrastructure.
Let’s first take a look at the security implications of working from home.
A study from Reeves and Rothwell, cited by the Brookings Institute, found that the number of Americans working from home doubled during the pandemic lockdown.
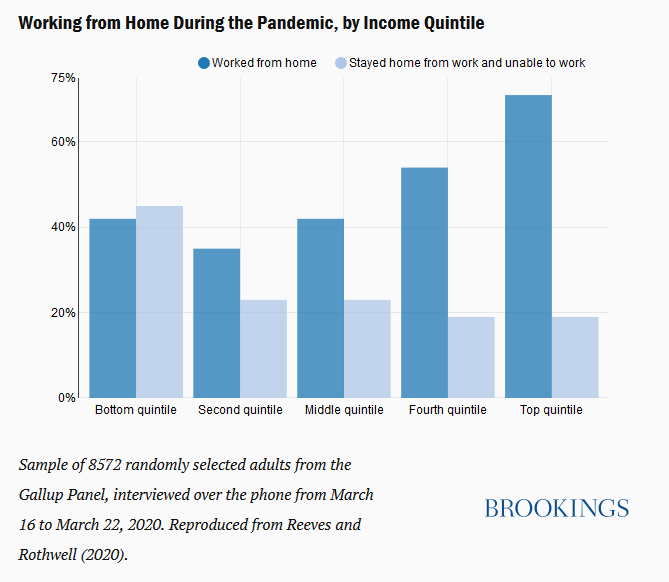
Some tech companies (Twitter and Square, for example) are allowing employees to telecommute indefinitely, but, as we’ll see in a moment, it’s not a money-saving move as one might first believe. Companies have to expend significant resources, replicating the support employees would normally receive in the office, to meet the demand of home office workers accessing corporate data from potentially insecure equipment and locations.
Given these costs, it’s no wonder that Facebook CEO Mark Zuckerberg believes that employees working from home will result in no net savings to his company: “The cost of supporting remote workers has generally offset the real estate and other costs of supporting people in the office,” he said on a Facebook livestream. “There are just different costs here. Remote workers need different benefits in some cases, including things like more tooling to make their offices work at home.”

What are the Increased Cybersecurity Risks Associated with Working from Home
During the Covid-19 pandemic, cyber-attackers have been targeting employees working from home who are eager to learn about the latest virus news from legitimate organizations.
Numerous fake websites and fake emails purporting to be from legitimate sources have popped up during the pandemic. (Cybersecurity company Mimecast has a timeline showing how these scams have evolved during the pandemic.)
While the call to action (e.g. related to the Coronavirus) may be new, the underlying criminal intentions are generally the same: to steal corporate login credentials or capture credit card numbers (usually via phishing), trick users into downloading a secret Trojan software or other malware to their devices, or demand payment via ransomware, including a new variation, “sextortion,” that threatens users with exposure of their supposed illicit web-visiting habits.
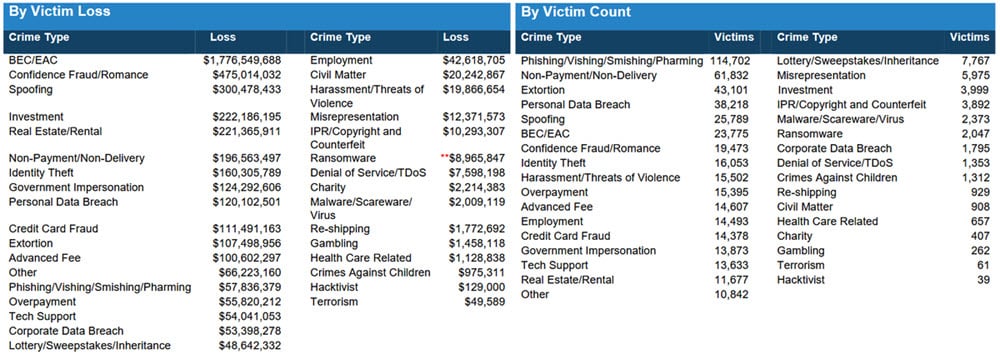
According to the FBI’s 2019 Internet Crime Report, one particular kind of online fraud is especially costly.
Business Email Compromise (BEC), also known as Email Account Compromise (EAC), scams were responsible for over half of cybercrime losses in 2019 (over $1.7 billion, averaging $75,000 per complaint).
BEC/EAC scams are a relatively low-tech attack with the potential for a big payoff. In one type of BEC scam, hackers craft a legitimate-looking email account (or present fake invoices or wire transfer requests) and send it to unsuspecting individuals, companies, or government agencies. The scam often fails, but when it hits, it can pay large dividends. For example, Galveston County in Texas paid over half a million dollars to a fake vendor posing as road paving contractor who requested a wire transfer payment be sent to a new bank account.
Like the FBI, the Internet Society has been tracking these scams; their most recent Cyber Incident & Breach Trends Report highlights these findings, which are broadly in line with the FBI’s numbers:
Telecommunication provider Verizon also keeps track of cybercrime activity, and their most recent Data Breach Investigations report gives important insight into how the incident rates for the most common breaches have varied over the past 6 years.
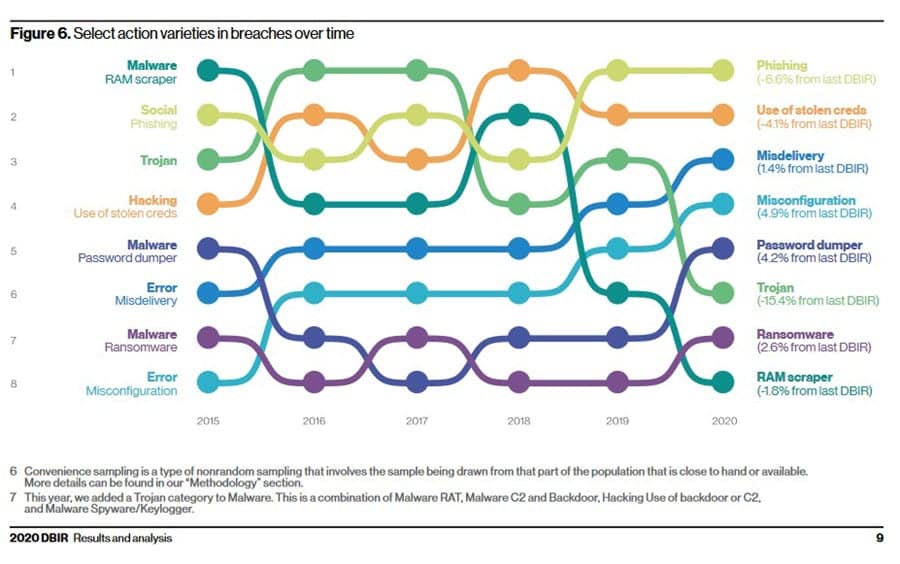
According to Verizon, phishing tops the list for 2020, which should be especially worrisome for corporate IT security teams, as remote workers are potentially more vulnerable to these type of scams, as they often access a mix of home and business email from the same computer.
If they have not done so already, security teams need to implement end-to-end systems that can track corporate email and lock it down; they also need to teach their workers the importance of not clicking on imposter emails designed to capture their login credentials or other important data, such as banking information.
But email is not the only vulnerable type of software application. As has been widely noted, video conferencing and chat systems have suddenly become mission-critical tools for home-based workers trying to carry out their jobs. Yet, many of these popular communication and groupware apps have also been compromised, such as Zoom (which was plagued by so-called “Zoombombing” attacks prior to its recent end-to-end encryption upgrade) and Facebook’s Whatsapp (which has become the target of a sophisticated spyware scheme.)
Risk to E-Commerce Providers Grow as Online Shopping Explodes During Lockdown
Just as the increase of people working from home has obliged corporate IT departments to step up their cyber surveillance activities to keep corporate data safe from cyber intrusions, e-commerce companies (and their various supply-chain partners) have also had to step up their game.
For online retailers, the whopping increase in online shopping has been a blessing and, in some unfortunate cases, a curse.
According to the cybersecurity firm Riskified, Target’s online sales doubled in Q1 2020 and Walmart’s online sales were up nearly 75%.
Yet most online merchants surveyed are woefully unprepared for a cybersecurity attack, with just over one quarter admitting they do not have measures in place to stop attacks.
Nonetheless, online attacks just keep coming.
For example, the cosmetics giant Avon suffered an as yet to be explained outage that took down much of its backend operations, shutting down the company’s ability to manage customer orders on its websites in the UK, Argentina, Brazil, Poland, and Romania.
While many attacks on e-commerce companies utilize well-known threats, some more recent attacks on e-commerce sites have become increasingly sophisticated, such as a new attack that leverages the knowledge that many companies’ content security policies (CSPs) often whitelist domains hosting their Google Analytics services, which in turn provides an opportunity for cybercriminals to break in by crafting a custom cross-site scripting attack with the goal of accessing customer credit card information.
David Capezza, the Senior Director of Payment Systems Intelligence at VISA, has called on merchants to step up their security activities, saying, “E-commerce merchants should know that becoming a victim is avoidable. For example, following basic cybersecurity hygiene and complying with payment industry standards such as PCI DSS (Payment Card Industry Data Security Standards) can help mitigate the potential of being compromised.”
Cybercriminals are Changing their Attack Strategies and Objectives
But, despite Capezza’s pronouncements, maybe it is getting harder to stay one step ahead of cybercriminals.
One reason is it’s not a static environment, the methods of attack and the motivations of cybercriminals are indeed changing over time. Speaking in a recent podcast, Geert van der Linden, the Cybersecurity services head of Cap Gemini, notes that the modus operandi of today’s cybercriminals is changing in three important ways.
Trend One: The Long Game
The first, van der Linden notes, is a shift from away from quick hit-and-run crimes (such as breaking into steal credit cards and passwords for quick resale on the black market then running away as fast as possible), to a more sophisticated preparation and waiting game, whereby criminal elements take their time planning and preparing for an attack — then pausing patiently until the right opportunity to strike presents itself.
This long game approach can be more lucrative for criminals and more devastating to organizations.
For example, hackers responsible for the 2017 wannacry ransomware attack (which hit the UK’s national health service particularly hard because many of their systems lacked critical security patches that had been issued over the previous 12 months) worked step-by-step to create a surreptitious worldwide network, which, once deployed, raked in millions of dollars from victims desperate to regain access to their data.
Stealing information and trade secrets is also part of the long game for cybercriminals; especially if the corporate security teams are unaware they have been hacked: the information gleaned from data sources can be sold on as regular updates and the newest trade secrets can be remarketed to unscrupulous competitors looking for competitive advantage.
Trend Two: Malicious Attacks
The second trend noted by van der Linden is a shift toward “molesting” or damaging the infrastructure of a single company, or even an entire country.
The Japanese automaker Honda is apparently the most recent victim of this type of attack.
This month, a computer virus forced Honda to shut down factories around the world, including in the US, Brazil, India, and Turkey, because they cannot communicate by email or perform remote exchange data with their internal servers. The American Honda Finance Corporation, which manages car financing, was knocked off-line too – as well as the systems that allow dealers to order repair parts or submit warranty claims. Some analysts have speculated that the attack involves the SNAKE Ransomware, which has the capability of forcibly stop Industrial Control System (ICS) operations and that the source of the intrusion might have been unwitting employees working from home.
(Once we get more information, this attack on Honda may fall into the same category as the infamous cyber-attack against Norsk Hydro, a ransomware attack that reportedly cost the company upwards of $75 million.)
Industrial manufacturers have not been the only victims of malicious attacks by hackers. State infrastructure has also been attacked, such as the infamous one that brought down the Ukrainian power grid in 2016 and the multi-day attack against the online infrastructure of the entire Estonian government in 2007. (Since that time, the Estonian government has created a world-class online infrastructure, which should be a model for the world to emulate.)
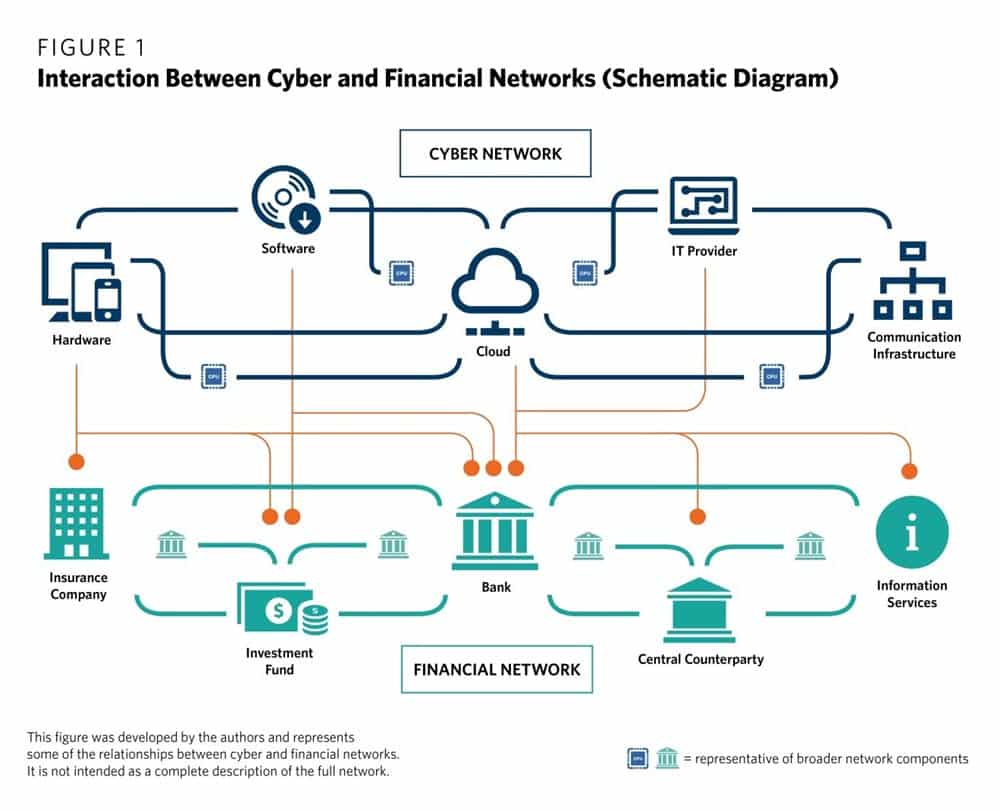
Cybercriminals that are motivated to create malevolence could also, potentially, put the world’s financial system at risk, where even a short outage can be incredibly costly.
For example, Germany’s once-proud FinTech startup, Wirecard, appears to be in the throes of some kind of financial fraud, with investigators unable to account for a missing $2 billion.
While this may or may not be related to cybercrime (it could just be outright fraud, time will tell), many analysts and researchers are increasingly concerned that a massive attack on our financial system infrastructure could lead to another worldwide financial crisis unless steps are taken now to reduce our exposure to cyber risk.
Trend Three: The Accelerating Speed of Cyber-Attacks
The final trend that van der Linden identified was the increasing speed of attacks.
Years ago, he notes, the timeframe for responding to an attack was in the order of months.
More recently, responding to an attack within 24 hours was considered acceptable.
However, in light of new technology, how comfortable are you flying in a “connected” plane or riding in a self-driving vehicle, knowing that the system could be infiltrated, sabotaged?
If a cyber intrusion takes control of the vehicle, you don’t have 24 hours to respond; you have to take action within seconds to avoid a potentially catastrophic accident.
The same concern for rapid response applies to our power grids (including nuclear power plants), our financial systems, manufacturing operations, and more.
IT Cybersecurity Experts Embrace a “Detect and Respond” Approach to Counter Cyber Intrusion
This need for a faster response is just one of the reasons that cybersecurity experts have dramatically changed their thinking about how to protect data assets over the past few years.
The original security model used by most corporations and governments was to build stronger and stronger defenses against what were deemed to be external threats determined to break in and steal critical data.

This “prevent/protect”-focused approach is often described in terms of a castle metaphor: to keep the “bad guys” out at all costs, the IT team needed to build a deep moat around the corporate castle, with ever taller and thicker walls, and exceptionally strong doors kitted out with hardened locks that are difficult to pick.
What does this castle approach look like in practice? In very basic terms, you might have a VPN-based proxy system protected by a corporate password that allows you to connect to your corporate network. Once you have been allowed through the front door, the castle model assumes you are one of the “good guys” and allows you to freely access all the corporate data services.
The flaws in this approach might be easy to spot. For example, think about Edward Snowden, who able to use his credentials as an NSA government contractor to access a wide range of secret government databases, which he downloaded remotely from his post in Hawaii – and the rest is history.
The “protect/prevent” castle model assumes that those on the inside are good, and the outsiders are bad. However, this approach is flawed when you realize that insiders are responsible for a healthy percentage of cybersecurity crime.
So what’s the alternative to the castle with high-security walls?
The new approach is a multi-layered model that places greater emphasis on “detect and respond.” The working assumption is that intruders will come in, but any suspicious behaviors need to be detected and responded to as fast as possible.
For this new approach to be successful, you need to have end-to-end visibility of the IT environment to track what’s happening.
A critical assumption in this approach is that no user is above suspicion; rather, they are invited into what is known as a Zero Trust Architecture environment, which challenges who they are at every step of the way (identity management) as well as ascertaining which systems this user can access (access management).
Unlike the “protect/prevent” castle with its high walls, users accessing a Zero Trust Architecture environment should not automatically be granted access to every data source; rather, each data source on the network needs to be separated into individual buckets, a topology known as “micro-segmentation.” This approach prevents users from wandering into areas where they shouldn’t be allowed.
Any user that makes a request to access one of these micro-segmentation areas needs to have their identity checked once again, and they should only be granted what is known as “least privileged access,” e.g. the minimum access needed to perform the job to which they are assigned.
From a user perspective, there may be some initial pushback. They might have to present their credentials multiple times (but with single sign-on, or SSO, the user experience can be streamlined somewhat), and most likely, they will also be required to use multifactor authentication (MFA), such as providing a code from a smartphone app, to gain access.

Cybersecurity is Driving Changes in IT Department Roles and Responsibilities
This approach also can be quite daunting for IT organizations as well. In a large enterprise, monitoring all user behavior in order to identify potential bad actors is, without question, a big data challenge. As a result, IT organizations are increasingly turning to artificial intelligence to processes user data in real-time to make decisions about which users have legitimate reasons for accessing data and which ones need to be locked out.
Also, network engineers designing network access controls or developers creating applications for Zero Trust Architecture systems need to change the way they’ve traditionally done their jobs. The new approach (known by some as DevSecOps and to others as SecDevOps) calls for developers and network engineers to bring security experts to the table during the initial project scoping and planning stages to ensure that security principles, such as micro-segmentation, are incorporated into new systems from the ground up – rather than tacked on at the end.
Also of note from a personnel perspective: as the body of cybersecurity knowledge increases, many network engineers and developers are brushing up their skills and obtaining specialized certifications, such as CompTIA Advanced Security Practitioner (CASP+) or (ISC)²’s CISSP. However, there is a still looming shortage of qualified security personnel: (ISC)2 estimates there is an immediate worldwide demand for over 1.25 million additional cybersecurity professionals. (Cap Gemini estimates this will grow to 3.5 million unfilled cybersecurity resources by 2021.)

The shortage of qualified security personnel is one of the primary reasons that many companies are partnering with managed security providers (MMS) who provide on-demand managed security services.
Cybersecurity concerns are also driving changes at the executive level as well. In addition to the traditional Chief Information Officer (CIO), many corporations are also establishing a separate role for a Chief Information Security Officer (CISO). The CISO role serves as a point person whose job it is to balance the competing interests of providing maximum security against the requirements to operate a business that is open to employees and customers (and does not have an unlimited budget to stop all potential cyber-attacks). As you can imagine, the CISO role can be crucial for companies trying to understand how to best apply resources to mitigate security risks, and, as such, it’s not unusual for CISO leaders to also hold a position on the corporate board.
Top Tips to Keep Your Organization Safe from Cyber-Attacks
1. Audit Who Has Access to Accounts and Eliminate Orphaned Accounts
Keep up-to-date on who has access to different parts of your network, starting with the on-boarding process of new employees (or contractors), as well as any changed access rules as they are promoted into different roles and responsibilities. Be sure to terminate any unused accounts (e.g. orphaned accounts) or access rights after employees or contractors have left a certain role or are no longer in service to the organization.
2. Regular Blocking and Tackling: Keep Patches, Firewall Controls, Antivirus, and Encryption Tools Up-To-Date.
Paying close attention to maintaining current, up-to-date software, firmware, and security patches for all your systems can pay dividends down the road by preventing cyber criminals from accessing your network using known exploits that have already been fixed by software and hardware OEMs.
3. Teach All Employees and Contractors How to Perform Safe Computing Operations
Poor computer security hygiene practices, such as loading software or USB storage devices from unknown sources, or clicking on suspicious email links, can have widespread, devastating consequences. Take the time to educate your employees and contractors on how to practice safe computing, such as knowing the warning signs for fraudulent emails and unusual wire transfer requests.
4. Use Multifactor Authentication, Micro-Segmentation, and Least Privileged Access
Implement the principles of Zero Trust Architecture by acquiring all users to use multifactor authentication (MFA) as well as limiting their access to the minimum resources required to do their job and nothing more. Compartmentalize your data sources (micro-segmentation) to prevent users from accessing data sources at will.
5. Conduct Practice Drills to Simulate an Actual Cyber-Attack and the Steps Necessary to Recover
As part of your business continuity planning processes, create a cyber-attack operational plan and conduct a full-scale exercise involving all employees, from the initial intrusion detection all the way through to recovering uncompromized backup files.
6. Apply Security and Backup Processes Used in the Office to Computer Systems Located in Work from Home (WFH) Environments
During the initial stages of the coronavirus pandemic lockdown, many companies were obliged to allow employees to work from home using computer systems that had not been inspected or vetted by IT security personnel. Make it a priority to transition from ad hoc security to standardized security procedures, including regular backup and virus scanning procedures.
7. Implement Artificial Intelligence Systems That Can Provide End-To-End Security Monitoring
Damage to corporate networks can take place quickly in an era of automated attacks. New artificial intelligence-based systems can identify and defend your network much faster than is possible by relying on human observation alone.
Formaspace Is Your Information Technology Partner
Turn to Formaspace for new ways of working.
Our custom furniture solutions, built right here in our factory headquarters in Austin, Texas, can provide your organization with a comfortable, ergonomic, and productive environment to work in, whether in the office or at home.
We can build custom solutions to help you expand your existing IT operations, or help you plan and deliver sophisticated furnishings for new information technology facilities.
Find out how we can help. Take the next step. Contact your Formaspace design consultant today and learn why leading tech companies, including Apple, Boeing, Capital One, Dell, Ford Motor Company, Google, Oculus, Toyota, Twitter, and SpaceX, choose Formaspace furniture solutions for their operations.