Major changes are coming to healthcare IT systems, including new rules mandating consumer access to health records via third-party applications, such as Apple Health. How can organizations entrusted with these sensitive records protect themselves from attack? We talk to cybersecurity expert Troy Newman to find out.
The COVID-19 virus outbreak is testing the capacity limits of the American healthcare system.
But it’s not the only challenge facing healthcare organizations across the country.
As the 2016 21st Century Cures Act moves into the implementation phase, healthcare IT departments will have to address some of the biggest regulatory changes since the Affordable Care Act first mandated the implementation of EHR (electronic healthcare record) systems back in 2010.
The new regulations are outlined in two documents issued from Washington in early March 2020.
The first is the CMS interoperability and Patient Access Final Rule (CMS-9115-F); the second is the ONC Final Rule, a massive 1,244-page document from Office of the National Coordinator for Health Information Technology (ONC).
Under these new rules, health IT teams will need to implement enhanced security measures (such as multi-factor authentication) to protect confidential patient data, while at the same time, eliminating anti-competitive “information blocking” practices that discourage transmitting data between different systems. Also included is a new Patient Access API requirement that patients be allowed to use any third-party application of their choosing to access their own health data — at no additional cost.
Introducing Troy Newman, Co-Founder of Cyber5
To find out what healthcare providers can do to keep protected patient information secure, we turned to Troy Newman, founder of Cyber5, a cybersecurity consultancy based in Houston, Texas.
Troy Newman was a recent guest speaker at IT Nation, where he outlined some of the best practices IT departments need to know when deploying Microsoft Office 360.
We began our interview with Troy by asking him why healthcare providers are so often targeted by cybercrime.
Q: Why are healthcare providers a top target for cybercrime?
It’s simple. Hackers want ePHI (electronic personal health information). This data is worth a lot on the Darkweb, and hackers want money.
In 2019, we saw report after report of medical institutions being hit with ransomware attacks that encrypted their IT system data, rendering them unable to operate.
Imagine if all the data on your computer was locked with a key that you didn’t have. These medical facilities simply couldn’t continue normal operations. And many of them had to pay the ransomer’s demands because they weren’t prepared in advance.
Q: What are the top cybersecurity risks facing healthcare providers?
While many executives and managers think the top cybersecurity risks originate from outside, you need to look first at what’s happening inside your organization.
I rank the top cybersecurity risks facing healthcare organizations this way:
Risk 1) Not educating your staff on the very real threat of cyber attacks.
Risk 2) Not having adequate monitoring in place to detect intrusions as they happen.
Risk 3) Not having proper systems in place to recover from a cyber attack.
Q: How can healthcare providers beef up their cybersecurity capabilities?
To answer this question, I’d start by asking if the audience is familiar with the NIST Cybersecurity Framework (CSF) and its five security components: Identify, Protect, Detect, Respond, and Recover.

It’s a complete framework for building a robust security program to protect technology infrastructure.
We start with Identify. We take a look at the business to understand where the “treasure” or “secret recipe” is. In the healthcare arena, this typically includes confidential health records.
This is how we identify what to Protect, e.g. which systems need extra protection from threat vectors.
Once you get IT systems protected, this is where Detect comes into play. We need to monitor and detect malicious traffic.
If an intrusion is detected, we have to be ready to Respond. Organizations need to write response plans and practice simulated drills before an attack. Plans should include a WISP (Written Information Security Program), a BCP (Business Continuity Plan), and a DRP (Disaster Recovery Plan).
Finally, after an attack, Recover comes into play, which allows the organization to recover data that has been compromised and resume normal operations.
All five components are necessary to protect your organization.
Q: How should organizations go about implementing the NIST Cybersecurity Framework (CSF)?
We always recommend that organizations start with an internal assessment to measure the security capabilities of their people, procedures, and technology.
To perform a consistent assessment, we created a Cybersecurity Maturity Grid, which is available for download on our website. Organizations are encouraged to review it to see how their existing security safeguards measure up.
From there, we recommend focusing your efforts in three areas, starting with the executive team.
Executive Buy-In and Identifying a Security Champion
Proper security requires executive-level support. Management needs to identify the organization’s risk tolerance and how thoroughly they want to prepare in terms of investing dollars and time.
The executive team also needs to identify a Champion (whether an individual or a team) to engrain cybersecurity into the culture.
Staff Training
The second area to focus on is staff training. Whether they know it or not, each and every staff member is responsible for the cybersecurity of the entire organization, so your employees need to be educated on the risks and consequences of cyber threats (from phishing to vishing) and to know this initiative is championed at the top executive level.

Infrastructure: Defense in Depth
Now let’s talk about tactics, e.g. what should be done on the technical side. This is where defense in depth comes in.
Organizations need to protect their perimeter with a true business-class firewall, then perform regular vulnerability scans of the network to identify weaknesses. Implementing a SIEM (Security information management) provides ongoing real-time threat detection.
Proper email security is also crucial. All email systems must have a front-end scanning solution to filter out malicious content (attachments or links). I also cannot overstate the importance of using MFA (multi-factor authentication). Email accounts are a key vector the hackers are using to compromise an organization. Once a hacker has breached an email account, they can act as that employee by emailing vendors, bankers, customers, and cause real damage to the organization. I also recommend that all organizations implement these basic email security tools: SPF, DKIM, and DMARC. These are no-cost security protocols that will protect your business when configured properly.
We cannot forget every endpoint, whether it’s a PC, laptop, or mobile device, needs to have several layers of protection. We recommend anti-virus, OS Firewall, APT (advanced persistent threat) detection, and Secure DNS.
Finally, all of these preventative and detection systems must be monitored by well-trained cybersecurity engineers.
Being prepared means creating an incident response plan and conducting trial runs that exercise the plan before you have a real cyber attack…

Q: When should healthcare providers consider turning to an external cybersecurity partner?
Threats from cyberattacks are on the rise, but many organizations find it challenging to hire cybersecurity professionals. Quality candidates are very much in demand, making it difficult to find recruits or justify the cost.
That’s why an increasing number of companies are partnering with cybersecurity consultants.
When we are engaged by a client, we see our function in terms of performing three roles:
Security Coach
Our first role is that of an organizational coach that helps prepare and train the organization’s executive and staff members to know how to help prevent cyber attacks.
Investigator/Detective
Our second role as a consultant is to serve as an investigator or detective, testing the organization’s infrastructure for vulnerabilities.
First Responder
Our third role is to be a first responder when things go wrong. We help spearhead the recovery after an attack so that organizations can quickly resume their normal operations.
Q: Thank you, Troy. As we close, can we ask you to tell us what makes a productive working environment for IT professionals?
That’s a really good question.
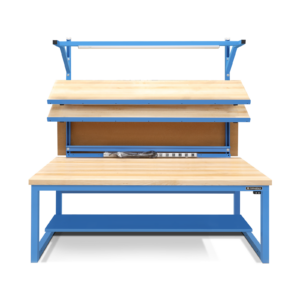
As we built out our new offices in Spring, Texas, three years ago, we wanted to go with enhanced ergonomic solutions.
We selected curved desks that wrap around each individual, with monitor arms to mount dual or quad screens.
And we recently configured an education facility with new electronic standing desks. We found these to be very comfortable; I like the ability to stand at times throughout the day.
Many thanks to Troy Newman of Cyber5 for sharing your insights.
To learn more about custom Formaspace furniture for your IT department, contact your Formaspace design consultant today.